Kaspersky
Threat Management and Defense
Advanced Protection powered by Threat Intelligence
Risk mitigation in an era of digital transformation
Digital transformation is key to future success for large organisations and government bodies. There are major benefits, but protecting a highly digitised infrastructure offers significant new challenges. The comprehensive Threat Management and Defense solution adapts to the specifics of your organisation and the ongoing processes of providing information security, enabling you to build a unified methodology for complete corporate protection against advanced threats and unique targeted attacks.
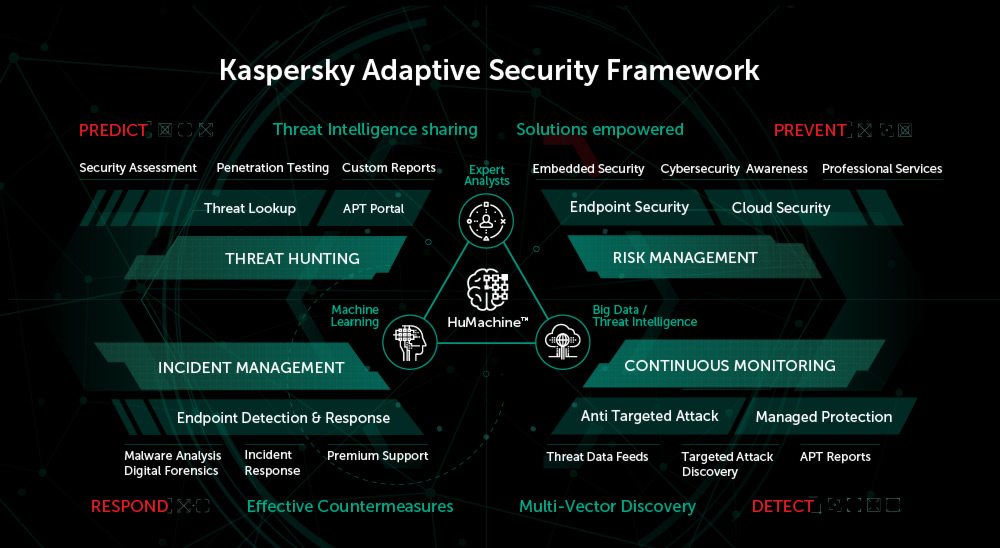
Kaspersky Threat Management and Defense delivers a unique combination of leading technologies and services which support the implementation of an Adaptive Security Strategy - helping your security team to Prevent most attacks, Detect unique new threats rapidly, Respond to live incidents and Predict future threats.
Suitable For
Kaspersky’s understanding of the inner workings of some of the world’s most sophisticated threats has enabled us to develop a strategic portfolio of technologies and services capable of delivering a fully integrated, adaptive security approach to enterprise sectors:
- Enterprise Organisations
- Government
- Financial Services
- Energy, Gas and Oil
- Telecommunications
- Retail

Adopting an adaptive security approach significantly reduces the risk of attacks and the resultant damage. Most threats can be identified through analytics and preventive technologies, while others are detected and rendered harmless much faster than through traditional approaches to protection. Kaspersky's Threat Management and Defense solution means you can develop and implement your own adaptive cybersecurity model right now.

The role of the Security Operations Center (SOC) isn't limited to identifying advanced threats. The SOC should be providing a full cycle of protection against targeted attacks: from counteraction and detection to response, elimination of vulnerabilities and forecasting of possible risks. Within the framework of Threat Management and Defense, Kaspersky offers a whole arsenal of security technologies and services for assistance at every stage of this cycle, helping to establish SOC efficiency.
Prediction and Prevention work to stop an incident before it evolves into an accident. Detection and Response define the discovery and remediation of an accident. In this paradigm, each subsequent stage requires greater resource consumption to react than it does in the preceding stage. Too often, security receives the budget it is perceived to deserve, not the budget it actually needs. Security must be highly prioritised and significantly invested in to ensure successful deployment and a strong RTO.
White Papers
Learn more, with thought leadership from globally recognised cybersecurity experts.
Targeted attacks, including Advanced Persistent Threats (APTs), are some of the most dangerous risks to your enterprise. But while threats – and the techniques cybercriminals use – are constantly evolving, too many businesses still rely on yesterday’s security technologies to protect against today’s threats. They are left exposed to:
-

The unpredictable results of a successfully compromised system
-

The lack of ability to respond to and qualify the modern threat landscape
-

A lack of visibility over corporate network and IT issues
-

A direct and reactive spend of up to $1m after a single incident
-

Stealth attacks: undetectable data and business process manipulation
-

A low outcome from investment into traditional security solutions






